EXCLUSIVE: Every economist on Mastodon just had their anonymity compromised by hackers from Yale University 🍿🍿🍿
Mastodon gets mastocucked!
Following these 3 articles…
Yesterday, my investigation was featured on Marginal Revolution:
https://marginalrevolution.com/marginalrevolution/2023/07/the-ejmr-doxxing-issue.html
And also on
’s Substack:The mainstream media also covered this story extensively (Inside Higher Ed, Associated Press, New York Post, Financial Times, Fortune, Bloomberg).
Twitter has spent the past 2 days freaking out. While it would be impossible to share the thousands of passionate tweets, I will highlight a few significant examples.
One noteworthy response came from a Berkeley economics professor who criticized my credentials rather than addressing the content of my investigation, a testament to the desperation of EconTwitter:
The most vile Tweet, as usual, came from Noah:
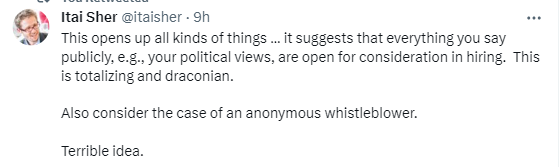
Jake Vigdor’s totalitarian-like response went the most viral:
https://twitter.com/JakeVigdor/status/1682439692200087552?s=20
Luckily, as you can see from the 129 QT's, he was ratio’d, almost exclusively from white male respondents. It's intriguing to note the silence in the QTs from female economists of color. Do WOC not care about free speech and anonymity?
David Bradford, the Busbee Chair in Public Policy in the Department of Public Administration and Policy at the University of Georgia, notably displayed a fundamental misunderstanding of his country's constitution:
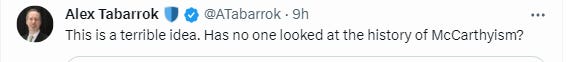
Jennifer Doleac's comments stood out as she explicitly declared her intent to use this data to attack her peers' careers.
She also plans to “guess” who owns EJMR. Note that she didn’t say “let’s identify Kirk”. She said let’s guess. Let’s start throwing around accusations with next to nothing to go on — this is acceptable on #EconTwitter:
Linking Mastodon to EJMR
A significant discovery is the connection between Mastodon and EJMR.
Yale holds IP data of anyone who posted on EJMR. We know that from the hack.
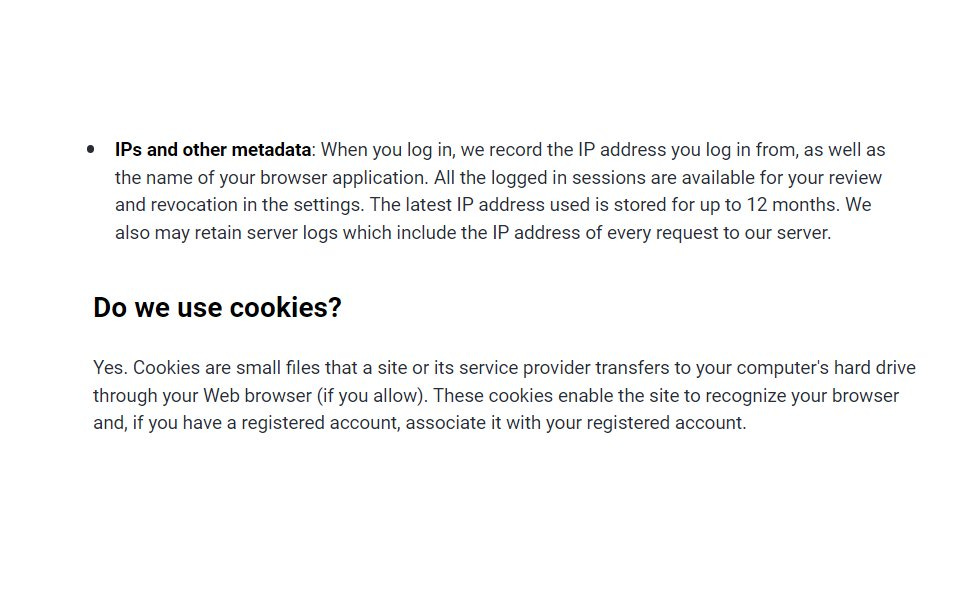
However, the IP data (and more) of those who posted on Mastodon EconTwitter, the econ profession's Mastodon server, is also owned by Yale.
This is because Paul Goldsmith-Pinkham, one of the Yale professors who hacked EJMR, moderates this Mastodon server:
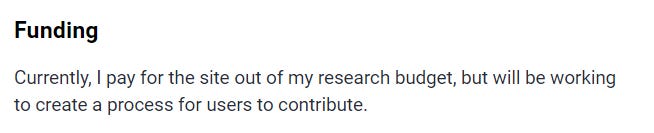
He funds the server through his research budget, making posters on his Mastodon server effectively his research subjects.
As per the platform's privacy policy, Yale owns your IP and cookies:
https://econtwitter.net/privacy-policy
This means that if you have posted on both Mastodon and EJMR from the same IP, Paul can link your Mastodon posts to your EJMR posts, compromising your anonymity. Ironically, this means that those leftists who most fervently cheered on the prospect of doxxing EJMR are now at risk of being doxxed themselves.
It seem transparency is a double-edged sword.
I hope nobody on Mastodon posted anything mean on EJMR, thinking they were anonymous. Prepare to be held accountable, Mastodon users.
As the adage goes, "Hell hath no fury like a plagiarist exposed."
It’s so obviously hacking the site. They exploited a security vulnerability. What else is hacking? As someone said, blowing a whistle at 2600 hertz was hacking .as sponser
— Anonymous
mastodon admins can see DMs as well. This is exactly the kind of guy you want to give that powerPGP has your "toxic" anonymous posts, linked to your IP, which is linked to the real name you used to sign up for his mastodon server. Can you see how this is different?Things are much dangerous than previously thought.
— Anonymous
If this is not NewSpeak, I do not know what NewSpeak is.
You can scrape all you want but decrypting the hash is illegally accessing stored private information. A version of illegal wiretapping.
— Anonymous
To give you an example, suppose you found out that Amazon inadvertently encoded user credit card numbers in a public facing website that could be scraped. The numbers were hashed but could be worked out with a lookup table attack. Is it OK for you to download the data, write a paper describing how to implement the hack, and then release the scraped data? Obviously not
— Anonymous
I think EconTwitterers are realizing nobody's playing anymore. Ppl really are screenshotting, and really are contacting IRB, and IRB really is investigating, and people really are talking to lawyers.
— Anonymous
he basically got his data by hacking into this websiteHow is burning cities to the ground not illegal? The regime permits what it permits.the law doesn’t apply to the left and its sympathizers and activists
maybe this episode will help teach naïve conservatives - or anyone concerned about things like free speech - about how power truly operates in the world
— Anonymous
Speaking only for myself, I am glad to know that, running 42 quadrillion attempts to back out identifying information does not count as "hacking." The new threshold must be 50 quadrillion
— Anonymous
I wonder if PGP had his own Zuckerberg style 'dumb f**ks' moment and will live to regret it.
— Anonymous
it is illegal, it's basically illegal wiretapping. See Electronic Communications Privacy Act (ECPA) 1986 Title II.
— Anonymous
These three guys hacked into a website and are laying the groundwork for a mass doxxing of people who anonymously posted deeply personal info, including information about their mental health and their martial problems. Sounds illegal. Yale and NBER are funding and hosting the project? Madness.
— Anonymous
I caught Florian stealing my bike off the rack in front of BU today. I ran up and he started sputtering something about the lock being publicly accessible and that he was just trying out combinations.
— Anonymous
https://en.m.wikipedia.org/wiki/Goatse_Security#AT&T/iPad_email_address_leak
> Group discovers AT&T inadvertently had been embedding subscriber emails in publicly accessible links.
> Brute forced this to scrape all links and uncover 100k subscriber email addresses and account IDs.
> Sent proof of this to Gawker, then AT&T to get them to fix the flaw they found
> Raided by FBI, charged and convicted with federal fraud and unauthorized computer access, nearly four years in jail
> After sentencing, member remarks that he is going to jail for "basic arithmetic"
How is this any different from what Florian and Paul did? Paul went to great pains to say they weren't hacking, just scraping public data, doing some mundane math, and getting IPs from it. In fact, Florian and Paul's approach was even more sophisticated since it involves not just trying every possible URL but running several quadrillion hashes. And Paul also said he was just using mundane math! Goatse Security consistently said their intent was only to uncover and fix security flaws. Paul and Florian never even reached out to Kirk when they found it and their intent was literally to doxx until IRB interfered with that, as their initial slides make clear.
— Anonymous
Thanks Florian/Paul. When you run a lookup table attack on 4 quadrillion rows using 2000 hours of compute time, that is taking advantage of a website's security vulnerability. No ambiguity there. The website owner incorrectly thought and claimed this would protect IPs, which are PII, also no ambiguity. You proved him wrong by reversing the hash. Reverse engineering the hash is absolutely hacking. I am eager for your day in court to argue your case. Have fun!
— Anonymous
The owner of EJMR agrees that this is a hack, according to an interview he gave to one mainstream outlet. In a groundbreaking move, he used ChatGPT as a neutral arbiter of truth:
Asked for comment Wednesday afternoon, EJMR sent an email saying, “you may wish to consider what a neutral actor (ChatGPT) thinks about the study.”
EJMR’s email then includes a question to that artificial intelligence program: “Would reverse engineering partial hash codes of thousands of website users to get their IPs with brute force be considered hacking?” ChatGPT, according to the email, replied “Yes, that activity would certainly be considered hacking, and more specifically, it would be illegal and unethical.”
I reached out to both Mastodon and the Yale authors for comment prior to publishing this article, but neither answered me. I will end this article by giving a platform to 2 anonymous EJMR posters:
Broette here. I reached out to the NYT.
Dear NYT,
I am a female assistant professor of economics and a frequent user of the controversial and “toxic” website EJMR. The recent study by Florian Ederer, Paul Goldsmith Pinkham, and Kyle Jenner covered by AP presents one side of the story, but there is another.
While it is indeed a toxic, sexist, and racist cesspool, EJMR is also a website where economists can whistleblow on research misconduct, and avoid retaliation (via paper rejections) by unethical economists at elite institutions.
A whistleblower revealed author Paul Goldsmith-Pinkham’s misconduct on the anonymous site, a situation where Paul stole another team’s published ideas. Then, this EJMR paper comes out, and this presents a severe conflict of interest since Paul had an incentive to know the identity of the whistleblower.
EJMR has called out much research misconduct and sexual harassment, especially against those at the top of the profession, who otherwise would not face consequences since they have the power to reject the papers of whistleblowers at top journals. Doxxing or getting careless with the data (Ederer jokes publicly on Twitter about a “bet” that he can identify original posters), or sharing it offline, etc, leaves the profession’s whistleblowers exposed to retaliatory action.
Other functions of EJMR include providing a social refuge for mentally ill economists. Mental illness is highly stigmatized in the profession, and graduate students sometimes make around 20K dollars a year (see recent Michigan graduate student Union controversy). They have no budget for formal therapy, and turn to EJMR to discuss the toxic behavior from the elites of the profession. I myself was bullied by a senior economist in graduate school, and I know the psychological toll.
The code and method alone provided by Ederer et al may allow others to replicate the study, and effectively doxx those who had legitimate complaints against their misconduct.
I fear I cannot publicly speak out against the dubious ethics of providing methods to de-anonymize the content of the website, even though I know that there will be collateral damage for both whistleblowers and for those struggling with mental illness. Even visiting the site has been stigmatized. But I assure you the consequences of the situation are grave. Sadly, visiting the site today, I see many promises of suicide, and broad speculation that releasing the data or methods will lead to suicide.
Feel free to reach out to me at my anonymous email address, lemonlemonlemon93@gmail.com, which I will monitor more closely than usual for the next few weeks, if you have any questions.
Sincerely,
A female assistant professor at a research institution who can look the other way on sexism if it means preserving the integrity of a discipline I am passionate about.
Here is the whistleblowing on Goldsmith-Pinkham’s work:
https://www.econjobrumors.com/topic/forthcoming-jf-by-yale-profs-is-a-rip-off-of-lrm-paper
Non-Yale IRB insider here.
Some advice to those who are contacting the IRB.
1. If you are willing, use your real name and work email. It's not that IRB don't take anonymous complaints, but if part of the framing of this paper is the authors vs a trolling site, it is easy for emails to be downplayed as trolling. I expect the IRB might be getting some pure troll emails, and you don't want to be lost in the shuffle. If you are doing it anonymously, then stick even closer to my other suggestions.
2. I would be careful about things like specific accusations of illegality. Unless you have consulted a lawyer, they have a lot more experience in this area of the law than you. There is a natural tendency to judge complaints by their least valid points, so if you make an obvious legal error it's easy for them to downgrade the importance of you.
3. Relatedly, don't go over the top. Stick to the known public facts (and provide the supporting evidence for those facts), limit speculation, and interpret everything in a measured way being charitable to all involved, including the authors, the IRB, posters on EJMR, and posters on Twitter.
4. Ask specific, relevant, and reasonable questions. That will get you out of the stock response world.
5. Consider making specific asks. A couple that come to mind are either the IRB or the authors making a public statement about the data privacy for this project. But make sure the asks are both reasonable and asked reasonably. Saying "I hereby demand you immediately fire the authors" will not get you anywhere.
6. Keep it tight and narrowly focused. It isn't a good forum to litigate everything (e.g. if you start talking to much about the pros and cons of EJMR, you are probably wandering down the wrong path).



![Yale University vows to 'geolocate' most EJMR users [PART 1]](https://substackcdn.com/image/fetch/$s_!QWM4!,w_140,h_140,c_fill,f_auto,q_auto:good,fl_progressive:steep,g_auto/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2Fe2921848-687a-4d6f-bdf8-d07ba7ea4be0_1343x647.png)
![Yale University vows to 'geolocate' most EJMR users [PART 2]](https://substackcdn.com/image/fetch/$s_!sKQV!,w_140,h_140,c_fill,f_auto,q_auto:good,fl_progressive:steep,g_auto/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2Fc78f22d8-d4cc-4824-b42c-bbeb03e76224_760x441.png)














My only comment is that academic economists and associated persons seem to have an awful lot of free time on their hands. It almost makes me think 'economics' is not a serious subject.
Didn't anyone use a VPN when they posted? I'll bet there are a lot of new VPN subscriptions these last few days.